Knowledge Center
Contribution of Eogogics Faculty and Inner Circle Members
Quantum Telecommunications Demystified
Introduction There is considerable concern that quantum computing will make existing communications security protocols obsolete. In particular, Public Key Infrastructure (PKI) methods are believed to be vulnerable using the Shor algorithm. This article seeks to familiarize the readers with the new quantum-based technologies and explore their impact on telecommunications, such as PKI. There is much…
The IoT and the Serious Security Risks It Poses
Introduction The Internet of Things (IOT) refers to the increasingly networked world we now inhabit, in which more and more “smart” devices use Internet to interact with other devices, servers, or with various users. It is not a new type of Internet, but an evolutionary development that shows how incremental technology growth can lead to…
Related Courses :
Distributed Computing for IoT: Data Management in a Fog Computing Environment
Mobile cellular operators are making plans for Mobile Edge Computing (MEC), which enables Cloud computing capabilities and an IT service environment at the edge of the cellular network. It is a concept developed by ETSI (European Telecommunications Standards Institute) that aims to bring computational power into Mobile RAN (radio access network) to promote virtualization of software at the radio edge. MEC brings virtualized applications much closer to mobile users ensuring network flexibility, economy and scalability for improved user experience.
Related Courses :
- Onsite Training: Emerging Technologies, SDN, NFV, Cloud, Blockchain and General Networking
- Onsite Training: 5G Wireless, M2M, IoT, SDN, NFV, Cloud
- Onsite Training: Defense, Security, Public Safety
- Onsite Training: IoT, IPv6, VoIP, EoIP, IMS, MPLS, SNMP
- Onsite Training: M2M, WiFi, Bluetooth, Zig Bee, IoT
Check out our courses on 5G Wireless technologies, applications, and marketplace along with related courses on M2M and IoT.
Blockchain and Other Cutting Edge Tech
Blockchain, the Distributed Ledger Technology behind Bitcoin, has attracted interest across many industries including financial services, legal, real estate, digital rights, identity management, healthcare, asset tracking, supply chain management, and the Internet of Things (IoT). A disruptive technology, it has the potential to transform the way many transactions are conducted.
Related Courses :
Contradictions: A Tool for Systematic Innovation
The Quest for a Killer App for Identifying Problems and Generating Solutions Through the first 20 years of my engineering career, I unsuccessfully sought the “killer app” for Systematic Innovation (“SI”). Each time I began employment with a heavy-hitter organization (such as the US Air Force Research Lab, Johnson and Johnson, Philips, and Intel…
Related Courses :
Optical Networking: Past and Future
Light-based methods have been used for information transmission for thousands of years. Probably the earliest method is the fires that have been used for signaling since Biblical times.Smoke signals have been used for communications for a long time, most notably by Native Americans. Lanterns hung in Boston’s Old North Church (“One if by land, and two if by sea”) figure prominently in Paul Revere’s famous midnight ride in 1775.
Related Courses :
Unleashing Engineering Creativity: The Kano Model
How do we decide which features to include in new products? That’s a great question. If we miss important features or include unnecessary features, customers will reject our products. If we include unexpected and exciting features, though, we can delight customers and jump ahead of the competition.
Related Courses :
The Internet of Things (IoT) Revolution: Are You Ready?
Nearly every industry vertical stands to be transformed by the coming IoT revolution. The IoT technology is creating enormous opportunities for new services as well as more efficient delivery of existing services. The rapid pace at which this technology is evolving is also giving rise to major privacy/security risks for individuals, institutions, and public infrastructure — creating new vulnerabilities and giving rise to not-as-yet-thought-of attack modalities, including those of remotely engineered death and destruction.
Related Courses :
SDN/NFV (Software Defined Networking, Network Functions Virtualization): Networking Game Changers?
The terms SDN (Software Defined Networks) and NFV (Network Functions Virtualization) have acquired magical connotations for those who work with networks but are not technical, raising many expectations. Are SDN and NFV really such a game changer for networking? SDN and NFV are among the half dozen or so technologies seeking to address the issues that trouble contemporary networks. The other major technologies in the mix include GMPLS, ASON, high-speed Ethernet, NGN, and OTN, with a good deal of overlap between the various solutions that have been proposed.
Related Courses :
The Internet of Things: Smart Devices, M2M, WSNs, and IoT
At its most basic level, IoT just connects simple devices over the Internet or other network which could be private and/or wireless. Common examples include the ‘program-from-anywhere’ thermostats and security systems already in use. At the mid-level, IoT is an enabler of new business and technology models, not just incremental improvement of existing ones. For example, autonomous vehicles will require very high levels of communication among devices in the vehicle (e.g., LIDAR, sensors, cameras, computers) and most likely devices/sensors outside the vehicle (e.g., other vehicles, fixed cameras, servers with detailed maps). At the highest level, the interconnection of devices could lead, over time, to new technologies that will reorganize the society, much as the automobile and the Internet have. One possibility is the “Smart City”, where IoT is used not only in autonomous vehicles, but where all types of transportation are linked to provide optimized people movement. Private self-drive cars, in this scenario, would rarely be needed. This could lead to entirely different land use patterns, for example.
Related Courses :
SDN/NFV: Enhancing Network Capacity and Functionality
SDN and NFV have been developed to help meet the challenge of increasing demand for services and user expectation of rapid provisioning and universal availability. Both rely on virtualization, the ability to make a piece of equipment look like another via the magic of software. SDN was originally developed to address the problems of large data centers, where virtualization of hardware and operating system is important. It will likely spread to other areas, including the WAN, where virtualization and the ability to dial up bandwidth and related characteristics would be extremely valuable as well. NFV is an outgrowth of SDN in many respects, concentrating on backbone networks, where the need to rapidly reconfigure resources is key.
Related Courses :
Mobile Backhaul “Mutual Fund” and Technology Trends
“I don’t follow any one mobile backhaul provider’s stock anymore, including my own – I just count the number of AT&T, Verizon and T-Mobile ads.” This comment was made by an admitted stock-a-holic who, it turns out, is a regional sales VP for a national backhaul provider.
MOOCs: A Revolution … or Just Plain Hype?
As of this writing, hundreds of MOOCs are being offered by US and foreign universities and millions of people have registered for them. But are they effective? They have been criticized for their lack of academic rigor. They also suffer from poor completion rates, with the bulk of participants dropping out in the first few days of the course. But they do offer the promise of making higher education and degrees accessible to a much larger chunk of the world’s population at a fraction of the cost, significantly reducing the cost of corporate training, and providing a convenient and cost-effective option for lifelong learning.
Mobile Backhaul: The Missing Link
Mobile is hot and mobile backhaul is thriving. As the number of mobile devices grows the need to bridge the gap between the subscriber devices and the IP cloud grows and as the bandwidth demand increases the demand for a bigger bridge between the subscriber devices and the IP cloud also grows.
Statistical Tolerance Analysis
Dimensional tolerances specify allowed variability around nominal dimensions. We assign tolerances to assure component interchangeability while meeting performance and producibility requirements. In general, as tolerances become smaller, manufacturing costs become greater.
Related Courses :
TRIZ: How to Stimulate Engineering Creativity Using TRIZ
TRIZ is an acronym for teoriza rezhinija izobretatalskih zadach, or the theory of inventive problem solving. The TRIZ technique was developed by Genrich Altshuller, a Russian navy officer who worked in the Soviet patent office. After reviewing 40,000 patents, Altshuller reached the following conclusions: Inventions and innovations follow common patterns that cut across industry and technology boundaries.
Related Courses :
GD&T Demystified
To better define a part, Geometric Dimensioning and Tolerancing (GD&T) is often used as a symbolic way of showing specific tolerances on drawings. GD&T is a valuable tool that effectively communicates the design intent to manufacturing and inspection.
Related Courses :
Obstacles to Creativity …. And How to Overcome Them!
Creativity obstacles can emerge as the result of structured thinking patterns, timidity, a fear of failure, resource myopia, fear of the unknown, overconfidence, personal and physiological factors, and not knowing how to be creative. This article outlines and recommends approaches for overcoming creativity obstacles.
Related Courses :
Good Mobile Backhaul: There’s No App for That!
Mobile backhaul and wireless backhaul are two names for the same thing: the communications link between the practically ubiquitous cellular antennas on radio towers, buildings, highway signs, church steeples, fake Sequoyah trees and elsewhere that connect mobile subscribers to the carrier IP network and/or Internet.
Our Comprehensive Mobile Wireless Backhaul Curriculum
Includes making a business case for backhaul, application case studies, market, technology deep-dive, and security
Unleashing Engineering Creativity
Creativity. We deem it essential for business and technical success, yet we are often puzzled about how to find it, how to empower our people to exercise it, and how to apply it. Do we need creativity for solving engineering or business problems, designing completely new products, improving existing products, or developing and improving processes? Are we born with creativity, or do we need to develop our creativity skills?
Related Courses :
Why a PM Certification Program May Not Translate into an Improved Project Success Rate
There are many possible roles in a project. The obvious ones include the project sponsor who pays for the project, the project manager (PM) who directs the project, and various project team members who perform project work.
Related Courses :
Eogogics Technical and Project Management Curriculum
This curriculum includes nearly two dozen courses on technical management, project management (including courses that meet the PMI certification requirements), engineering economics, cost reduction, and related management topics.
Engineering Education in Exotic Places
I count myself as one of the lucky people for many reasons, but one of the top reasons is my work with Eogogics Inc. I travel to some fairly exotic locales as an Eogogics faculty member, and I see parts of the world many folks do not.
Decision-Making Tools and Expected Monetary Value (EMV)
Decision-Makers’ Toolkit “Decision-making is the cognitive process of selecting a course of action from among multiple alternatives. Every decision-making process produces a final choice.” That’s what Wikipedia says anyway. What it doesn’t say is that some decisions must be made for outcomes that will occur in the future. However, there are a couple of…
20 Hot Technologies for 2012: The Indirect Evidence
The F-117 Nighthawk stealth strike aircraft was a remarkable achievement: an aircraft so stealthy that its invisibility allowed adversaries to detect it. How? From indirect evidence.
Computing in the Cloud: A Practical Review
Cloud computing appears simple but is very complex. The apparent simplicity has caused many organizations to move to cloud computing somewhat blindly, driven largely by promises of simplification which will result in cost savings, or just sheer cost savings. Cost savings alone is often enough cause for celebration. And, interestingly, the results achieved by those organizations who “just go for it” are, unexpectedly, usually very positive.
Related Courses :
Evolution of Mobile Positioning and Location-based Services (LBS)
Mobile positioning and location-based services (LBS) have come a long way since the FCC order for phase II of 9-1-1 dictated that cellular operators provide location of emergency callers within a certain degree of location accuracy.
Related Courses :
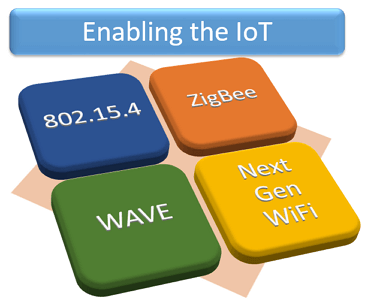
IoT-enabling Technologies: IEEE 802.15.4, WLLN, ZigBee, WAVE, Next Gen WiFi
Eogogics IoT-enabling Technologies Workshop The Internet is rapidly turning into a hyper-connected network of tens of billions of computers, smart phones, homes, buildings, vehicles, products, appliances, devices, machinery, and sensors. The Fifth Generation of Wireless (5G) is being engineered for such massive interconnectivity, but it will be aided by technologies such as LR-WPAN, WLLN,…
Related Courses :
Cyber Security: Next Pearl Harbor?
A spate of cyber-attacks, some of which were quite serious, have recently affected government agencies as well as businesses in a wide range of industries, including the CIA, US Senate, IMF, NATO, Google, Lockheed Martin, Sony, Citigroup, and others.
Related Courses :
What I did on World IPv6 Day
Thursday, June 8th, 2011 was the Internet Society’s World IPv6 Day. Years from now will you remember where you were and what you were doing on this important day? While the events of World IPv6 Day are not etched as deeply into my memory as, say, the day Ronald Reagan was shot or the day…
Technology and Society: The Changing Landscape
Technology and Society: Introduction In the halcyon days of technology development, just a few decades ago, advances were greeted with enthusiasm. Everyone expected a better life from new devices: computers, microwaves, and nuclear power, to mention a few. Environmental concerns, global warming, worker displacement, Intellectual Property Rights (IPR), energy conservation, and globalization were not on…
Related Courses :
MPLS and the Evolving Telecom Landscape
By 2010 both ATM and FR were in fairly steep decline, relegated to the status of legacy technologies. MPLS usage is growing and new applications for it continue to emerge, making it the technology of choice for most large-scale networks. Nowadays the great buzzword is “cloud computing”, with different versions such as Software as a Service (SaaS—Gmail, Google maps, YouTube, Facebook), Platform as a Service (PaaS—Amazon Elastic Compute Cloud, Windows Azure, Salesforce). All of these utilize MPLS-based networks.
Related Courses :
“When It Comes to Web 2.0 and Next Gen Communications, I’m with Tim … Pretty Much.”
Timothy Berners-Lee invented the browser and, subsequently, the World Wide Web. The impact of this browser thing of his is so profound that not only does it transform the way that everyone in the industrialized world interacts with each other, it inspired Her Royal Highness Queen Elizabeth – with but two taps of the royal sword – to transform Mr. Berners-Lee himself into Sir Timothy.
Related Courses :
Root Cause Failure Analysis: Reducing Costs and Increasing Customer Satisfaction
You know the problem: You’ve had a product in production for years with recurring failures you can’t seem to stop. Your people say it’s inherent to the product, and there’s nothing you can do about it. Production continues and so do the failures. You get to watch a sizeable chunk of your profits continue to move from the production line to the scrap bin.
Related Courses :
Eogogics Reliability Engineering Curriculum
This curriculum offers courses and workshops on FMEA, Root Cause Failure Analysis (RCFA), Design of Experiments, and Industrial Statistics, besides an overview course on Reliability Engineering.
Do You Support Eunuchs?
Members of the press waited along with company executives and industry dignitaries for the long-anticipated unveiling of the WANG Professional Computer. The newest member of the WANG Laboratories’ computer family was a “blazing fast” MS-DOS machine boasting a 16 bit processor and up to 640 kilobytes of memory – “the most memory”, I recall Bill Gates saying – “that would ever be needed”. The date was April 5th, 1983.
IEEE WCET Course: WebLive™ on Jan 31 – Feb 10!
“WCET1” is one of a pair of Eogogics courses tied to the IEEE Wireless Communication Engineering Technologies curriculum: It covers such RF (physical layer) topics as ….
Related Courses :
Supplier Competition: A Great Tool for Reducing Cost
How long has it been since your suppliers felt competitors chasing their business? If you have to think deeply to remember when you last made your suppliers compete, it’s been too long.
Related Courses :
5G, M2M, IoT …. Systematic Innovation Using TRIZ
We kicked off our innovation curriculum in 2015 with a MOOC (Massive Open Online Course) attended by hundreds of engineers worldwide. While many innovation methodologies are creativity stimulation techniques rooted in psychology, TRIZ turns inventing into a systematic, algorithmic process. We teach both types of courses, but the demand for TRIZ has grown steadily, making our TRIZ curriculum grow over the years as well.
Web Classes: NGN, MPLS, IMS, SIP, VoIP, EoIP/VoIP, IPTV, 3G LTE/4G, WiMAX, OFDM, MIMO, SDR, FMC ….
“Why don’t you offer online classes on emerging telecom technologies, so those of us who’re too busy to travel to public classes can keep up with the industry?” asked a fellow telecom exec in a recent conversation. “Aren’t there plenty of companies already offering free webinars?” I asked. “Yeah, but it’s not training. They’re all selling something: hardware, software, tools, or whatever” he countered.
Related Courses :
Technology and Society: AI, Robots, Drones, and People
If you enjoy science fiction, as I do, you know that it’s replete with visions of worlds enabled by technology, both utopian and dystopian. A world without hunger or disease on the one hand to one reduced to a post-apocalyptic state by nuclear, biological, or cyber warfare or by a “technological singularity” (where, e.g., the…
A “Cheap” Second Opinion
The nature of much of the “training” that Eogogics does has been changing over the last twelve months. I hadn’t really noticed it until a training client brought it up. “This training session is really great”, he said. “It provides a “cheap” second opinion on a lot of our development directions.”
Broadband Technology Opportunities Program (BTOP) to Spark Next Telecom Boom
The Broadband Technology Opportunity Program (BTOP), created by the American Recovery and Reinvestment Act of 2009 (aka “Stimulus Act”), provides almost $5 billion in grants from the National Telecommunications and Information Administration (NTIA).
Ya Can’t Risk Something This Important, Mate.
“It’s not gum, that’s for sure. Looks like sports drink and it’s been here a while.” Is this the opening scene from a CSI TV show? Not quite. I had boarded the Sydney City Rail train at Central Station bound for Green Square. Morning commuters juggled their cups of coffee, newspapers and PDAs.
Who Is Listening?
We hear a lot about the privacy and security of cellular conversations. Most of the focus is, knowingly or otherwise, on the vulnerabilities inherently present over the air-waves. Most laymen, unfamiliar with the availability and usage of encryption techniques, look at the problem very superficially.
Related Courses :
SOX and Other Compliance Training Bugaboos!
Government regulations and business best practices dictate that you not only conduct certain courses but also maintain records to show that they have been taken and understood by all concerned. Not offering such training can jeopardize the health and safety of your workers, earn the ire of your shareholders, and/or get you on the wrong side of the regulatory authorities.
Related Courses :
VoIP QoE, Ken Lay [formerly] of Enron, and “Photographic Evidence”
On the left side of the screen was Ken Lay being led off in hand cuffs. On the top was a quote from Mr. Lay: “But I told him to pass the books … not to pad them!”.
Related Courses :
What’s Your (Myers Briggs) Type?
Jung noted that we’re always either taking in information (perceiving) or organizing that information and drawing conclusions (judging). Perceiving can involve sensing (what is) or intuition (what could be). Similarly, judging can involve objective considerations (thinking) or its impact on people (feeling).
Related Courses :
Eogogics Professional Development Curricula
Three Views of Quality of Experience
From the late 1700s to the early 1800s, the Japanese wood block artist Katsushika Hokusai created forty six wood block prints and, for reasons understood only by the artist, entitled the collection “Thirty Six Views of Fujiyama”.
Power Up! With Eogogics’s Cutting-Edge Courses and Research Publications.
Check Out Our Cool New Website! Besides its fresh look-and-feel, it offers many new courses, research publications, articles, streamlined navigation, and faster load. It’s now open-access, no login needed. So read on, and do take a moment to take the new site out for a spin. If you spot something interesting or if we can help you find something, give us a shout (+1 703 345 4375) or drop us a line (info@eogogics.com).
The Three C’s of VoIP: CODECS, Codes, and Convicts!
Anyone who has ever been engaged most certainly can list the four “Cs” of diamonds: Color, Clarity, Cut and Carat weight. But did you know that there are also three “Cs” of Voice over IP?
Related Courses :
Eogogics Courses on Multimedia Technologies
Check out our multimedia curriculum for courses on IMS, SIP, VoIP, and EoIP.
Knowledge Make-Overs: Why Not IPv4/v6?
The fad these days is make-overs. The first in the trend were fashion make-overs where some hideously unattractive and under dressed person was transformed, through the miracle of modern cosmetology and fashion science, to a hideously over-made up and over-dressed person.
Check Out Our IP Curriculum
It covers IoT, IPv6 implementation, TCP/IP, Mobile IP, IP Security, BGP, MPLS, and more.
MRI Is to Medical Diagnosis as Wireshark Is to Network Traffic Analysis and Troubleshooting
I really enjoy watching the TV show House. Not for Hugh Laurie’s award-winning sarcasm – which I find formulaic and annoying – but, rather, to watch the diagnostic process unfold. House is truly unique because the real star of the show might turn out to be leishmaniasis or schistosomiasis rather than Brad Pitt or George Clooney. I watch the team meetings and brainstorming with great interest, the whiteboard filling with symptoms, while the team postulates the cause.
Digital Image Processing in Today’s Connected World
Photography — like audio, video, telephony, and most other forms of communication — went digital many years ago. Digital images, whether from digital cameras, the Internet, or software programs, are used in nearly every industry as well as in science and technology, medicine, education, and many other areas. Because the images are digital, a vast…
The Internet of Things (IoT) Revolution: Are You Ready?

Powered by the expansion of connectivity fueled by IPv6, the Internet is quickly morphing from a ‘network of computers’ into a ‘network of things’, and this technology is developing at a much faster pace than other such technologies of the past. Smart phones, cars, homes, buildings, wearable computing devices, unseen but ubiquitous sensors embedded into appliances, equipment and infrastructure, and many other “things” (including living things such as cattle and wildlife) are all getting linked up into a vast and pervasive Internet of Things (IoT)! It’s a disruptive technology that — though largely invisible to consumers — will have profound impact on our everyday lives, how businesses operate, and on the world economy as a whole (multi-trillion dollars) — all in as little as five to 10 years.
Related resources:
Article: Distributed Computing for IoT: Data Management in a Fog Computing Environment
Course: Internet of Things Workshop
Research publications on IoT (look for ‘IoT’ in our Store‘s ‘Search Product’ field)
Nearly every industry vertical stands to be transformed by the coming IoT revolution. The IoT technology is creating enormous opportunities for new services as well as more efficient delivery of existing services. The rapid pace at which this technology is evolving is also giving rise to major privacy/security risks for individuals, institutions, and public infrastructure — creating new vulnerabilities and giving rise to not-as-yet-thought-of attack modalities, including those of remotely engineered death and destruction. Yet, many businesses and government agencies wonder if this is all passing hype — which it is not — and many do not know how the IoT should fit into their organizational strategy.
So is your organization positioned correctly to benefit from this coming Internet of Things (IoT) revolution? Starting with this issue of the Eogogics Quarterly, we will be publishing a series of articles, courses, and research publications to help our readers better understand the underlying technologies, business and societal impact, potential, and market landscape of the Internet of Things (IoT). Featured in this issue are an article on distributed computing for the IoT and an update on the new courses and research publications on IoT that have been recently added to our product line-up. Are there IoT issues you’re interested in that are not covered by our courses and research publications? Call us (+1 703 345-4375) or drop us a line at info@eogogics.com. We may be able to help.