The Internet of Things: Smart Devices, M2M, WSNs, and IoT
Internet of Things (IoT): An Introduction
Check out our IoT, M2M, and 5G curricula as well as the related market intelligence publications in our online Store.
The “Internet of Things” or IoT refers to the increasing network connections and interaction of “smart” devices. It is not a new type of Internet, but an evolutionary development that manifests how incremental technology growth can lead to qualitative societal and business change. Many readers will recall how the Internet changed the way we do research, the way we buy things, and the way we interact, just to name a few, and thus the nature of society. This was the result of the proliferation of computers and smart devices, as well as ever cheaper and more available bandwidth. The Internet upended many business models and led to the explosion of social media; but it was—and is—primarily a person-to-server or person-to-person mechanism. IoT on the other hand involves device-to-device communications. There are many devices that could be connected and interact, on scales ranging from tiny low-power sensors to high-power devices with powerful CPUs and large memory. IoT spans this range, but utilizes other technologies to help it.
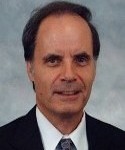
There has been explosive growth in connected devices, as shown in Figure 1:
Figure 1. Growth in Connected Devices
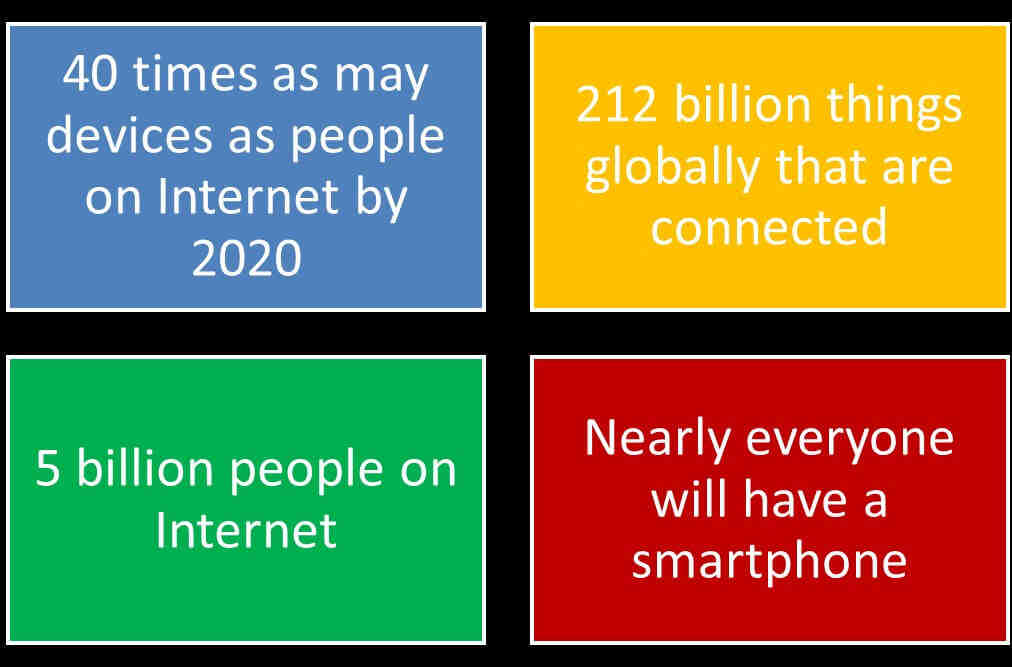
In the early days, most Internet traffic was the result of someone sitting at a computer terminal connected to the Internet requesting a service, such as email or a document (later a web page), from a server also connected to the Internet. Technically this is machine-to-machine, but it is controlled by a person. With IoT, there is no person involved and the devices talk to each other. Of course the hardware to allow machines to send data over the Internet has been around for a long time. What is changing is the ubiquity of these machines, the low cost of the Internet interface, and our increasing ability to program the machines to take over tasks that we used to do manually, using connections over networks. The IoT marketplace is expected to grow dramatically over the next few years, as shown in Figure 2:
Figure 2. Market Size for IoT
IoT and Other New Technologies
M2M: Machine-to-Machine Communications
One of the new technologies that’s part of the Internet of Things is Machine-to-Machine (M2M) communications. M2M, though not well-defined, is a set of methods and protocols to allow devices to communicate and interact over the Internet (or other network) without human intervention. M2M is sometimes considered to be low-overhead short-range wireless communication between machines, utilizing protocols with much less overhead than full-blown TCP/IP. Many M2M applications involve low power wireless devices with limited computing power and narrowly-defined functionality. Low-overhead protocols have been devised for them, including Message Queue Telemetry Transport (MQTT), Constrained Application Protocol (CoAP), and Open Mobile Alliance Light Weight M2M (OMA LWM2M). CoAP is actually a specialized web transfer protocol designed for applications such as smart energy and building automation. There is, of course, no reason why IoT devices cannot use high-powered CPUs and wide bandwidth, and in many applications this is clearly necessary, such as smart cars interacting with external servers. So IoT spans a huge range from very simple low-powered specialized devices and sensors with low bandwidth needs to complex, high-powered devices in large high-bandwidth environments.
WSNs: Wireless Sensor Networks
IoT configurations often involve sensors, which can be connected by wireless networks. Such sensor networks are termed “Wireless Sensor Networks” or WSNs. A WSN comprises spatially distributed autonomous devices equipped with sensors, connected through a wireless network to some type of gateway. The sensors typically monitor physical or environmental conditions. The gateway communicates with another set of devices that can act on the information from the sensors. Application examples include patient monitoring; environmental monitoring of air, water, and soil; structural monitoring for buildings and bridges; industrial machine monitoring; and process monitoring. The wireless network could be WiFi or Bluetooth, and the protocol one of the three listed above.
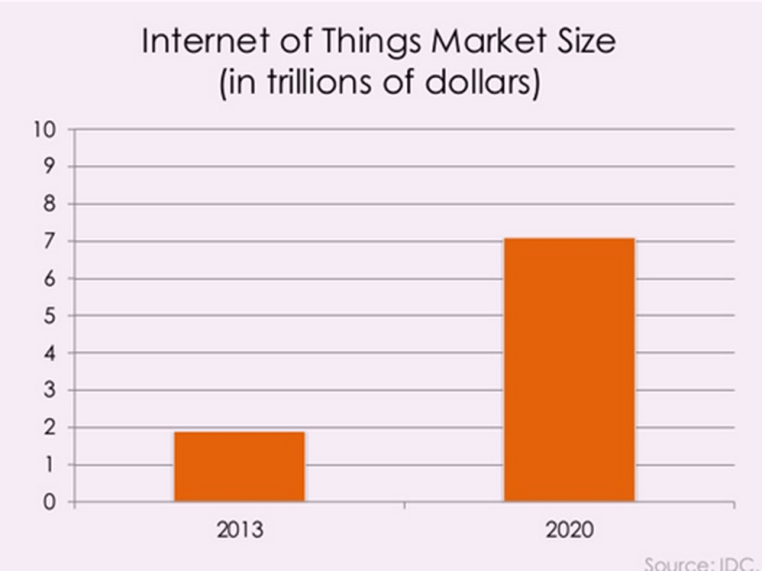
The boundaries between these networks are not clearly drawn, and in practice they overlap considerably. Figure 3 shows the relationship schematically:
Figure 3. Relationship of IoT, M2M, and WSN
For the purposes of this article, we will regard M2M and WSN as forming part of IoT.
Goals of IoT
In the short term, at least, the goals of IoT are straightforward, as illustrated in Figure 4:
Figure 4. Goals of IoT
The objectives revolve around efforts to reduce costs and save time. But they also promise to make new things possible that are not feasible now, such as devices for improved patient monitoring and improved transportation systems utilizing autonomous vehicles and other modes.
IoT Enabling Technologies
There are many technologies that support IoT and make possible its steady advance. A partial list includes the following:
- Cheap and ubiquitous telecommunications
- Smart software
- Smart devices
- Cheap memory
- Cheap and extremely powerful microprocessors
- Cloud Computing
- Big data, event stream processing, real-time analytics
- Machine Learning
- Wireless sensor networks
- Low power short-range and wide area wireless networks
- Embedded systems
- Automation and control Systems
- Existing and emerging telecom technologies: Li-Fi, LPWAN, LTE-Advanced, 5G, WiFi-Direct, BLE, ZigBee, Z-Wave, Thread, HaLow, …
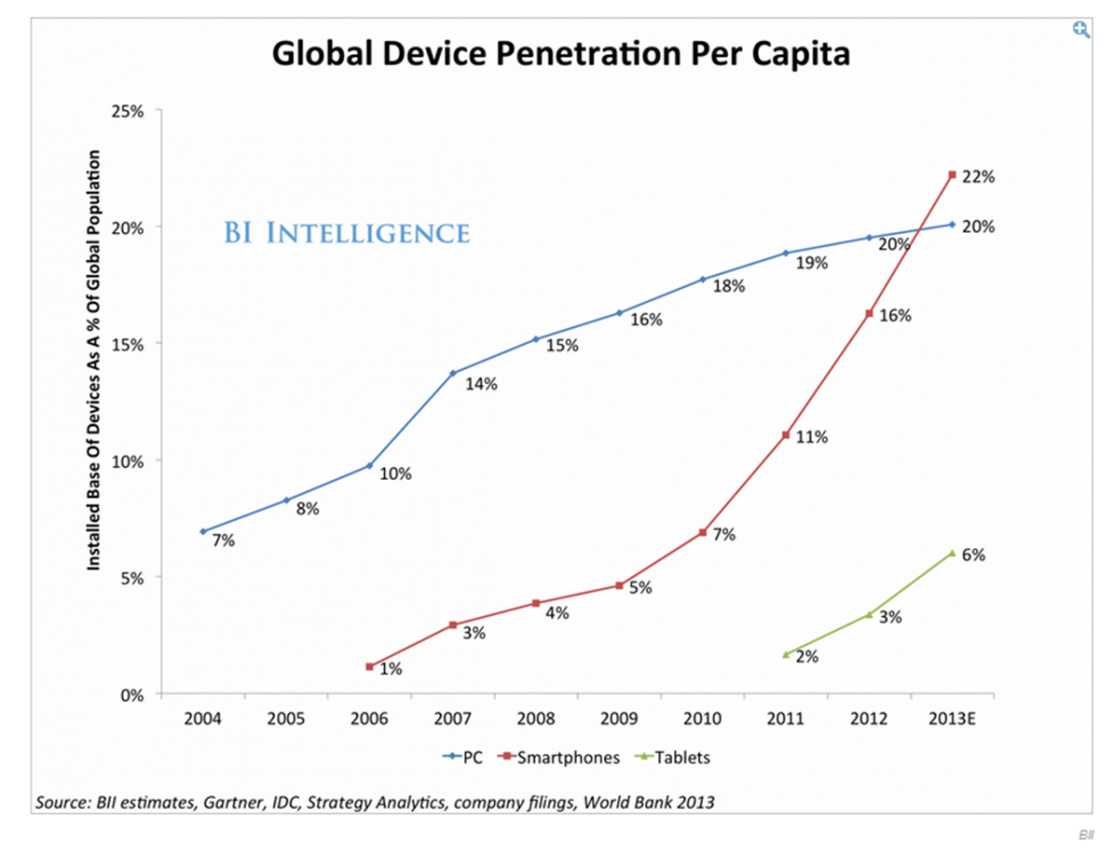
Few of these are radically new; most represent ongoing improvements to existing equipment and software. IoT is one of the beneficiaries of these continual improvements and cost reductions. Smartphones, for example, are clearly central to many IoT applications. The rapid growth of these devices is one driver for IoT:
Figure 5. Global Device Penetration
Understanding the Vision of IoT
IoT can be understood on three levels:
At the lowest or most basic level, IoT just connects simple devices over the Internet or some other network, which could be private and/or wireless. Common examples already in widespread use are programmable thermostats (change your house temperature at anytime from anywhere in the world) and security systems. Most modern security systems allow you to monitor your home security cameras over the Internet with a special App. Here is a typical system, this one by Honeywell and sold (of course) over the Internet by Amazon:
Figure 6. Home Thermostat Control over Internet
At the mid-level, IoT is an enabler of new business and technology models, not just incremental improvement of existing models. For example, autonomous vehicles will require very high levels of communication among devices in the vehicle (e.g., LIDAR, sensors, cameras, computers) and most likely devices/sensors outside the vehicle (e.g., other vehicles, fixed cameras, servers with detailed maps).
At the highest level, the interconnection of devices could lead, over time, to new types of technologies that will reorganize society, much as the automobile and the Internet have done. One possibility is the “Smart City”, where IoT is used not only in autonomous vehicles, but where all types of transportation are linked to provide optimized people movement. Private self-drive cars, in this scenario, would rarely be needed. This could lead to entirely different land use patterns, for example.
IoT Application Areas
There are many possible application areas for IoT. Just to name a few, consider:
- Retail
- Healthcare
- Wearables
- Smart home
- Smart cities
- Intelligent transportation
- Smart grid
- Smart agriculture
- Smart industry
- Energy management
Here are two examples:
Figure 7. Smart Sprinkler Control over the Internet
Smart sprinkler control is a rather obvious idea; this model is from lono.io. The following glucose monitoring system from www.telcare.com could be extremely beneficial to many diabetes patients:
Figure 8. Glucose Monitoring Using Smart Devices
IoT Security
Obviously the future viability of IoT will depend on the degree of security attainable. The more we automate the systems upon which we rely for our daily life, the more vulnerable we become. Already this is an issue not only with autonomous cars—where the potential for mischief is obvious—but even with cars already on the road, due to their computerized infrastructure that can be controlled, to some extent at least, by wireless signals. Control of vehicles by hackers reportedly has already happened. And what if a hacker took over your car (with you in it) and drove it to a remote location, where you were forced to give him your bank account information or your car would go over a cliff?
Last year, there was a large cyber-attack that utilized smart devices, the type employed by IoT systems. According to the Wall Street Journal,
Attackers used an army of hijacked security cameras and video recorders to launch several massive Internet attacks last week, prompting fresh concern about the vulnerability of millions of “smart” devices in homes and businesses connected to the Internet…Experts have long warned that machines without their own screens are less likely to receive fixes designed to protect them. (“Hackers Infect Army of Cameras, DVRs for Massive Internet Attacks”, Drew Fitzgerald, WSJ, 29 September 2016)
That is, people tend to forget about smart devices, and the more out-of-sight smart devices there are in the IoT, the more vulnerable we become. This problem is, I’m afraid, not receiving as much attention at this moment as it should, and this will probably take many years to fix. Of course, 20 years ago, when the Internet was just getting started as a commercial venture, security wasn’t given much thought either. But there is a difference if we don’t have a screen with which to interact with smart devices. When was the last time that you updated the firmware in your thermostat, or for that matter, your car?
Any mid- or high-level IoT-mediated changes will require new security paradigms, and these paradigms will no doubt add overhead to the IoT, and may slow its deployment.
Summary
The Internet of Things is coming and indeed in some ways is already here. It encompasses the networking and interaction of smart devices to achieve functionality that is currently labor-intensive, inconvenient, or just not feasible. It has begun with small-scale smart devices, and is progressing through larger, more complex systems such as autonomous vehicles. At some point in the future, the scope and degree of the automation may result in changes in major areas of society such as living and transportation, much as the automobile and the Internet have done. However, a major barrier to all of these applications is security, because anyone who can seize control of networked devices can create havoc and even cause personal injury or death.




Sorry, comments for this entry are closed at this time.